Original source: GigamonTV
This video from GigamonTV covered a lot of ground. 7 segments stood out as worth your time. Everything below links directly to the timestamp in the original video.
As companies rush to integrate AI, understanding the hidden dangers—from insider misuse to advanced cyberattacks—is crucial for safeguarding your organization's data and compliance.
AI Adoption in Latin America Faces Major Security and Regulatory Risks
The rapid adoption of Artificial Intelligence (AI) in Latin America introduces significant security vulnerabilities, according to Óscar Acosta. Key risks include "Shadow AI," where unauthorized use of AI tools by employees leads to sensitive data exposure and potential regulatory non-compliance, with financial impacts potentially reaching millions. Additionally, AI itself is being leveraged by attackers to create more sophisticated threats, such as deepfakes, advanced phishing, and ransomware, making traditional detection methods less effective.
These evolving threats, coupled with blind spots in monitoring lateral traffic within microservices and containers, highlight the critical need for robust network telemetry. This technology provides the necessary observability to detect and mitigate AI-powered attacks and unauthorized AI usage, preventing substantial financial losses and productivity impacts, while also aiding adherence to developing regulatory frameworks like MITRE ATLAS for AI security.
"The AI itself can be powerful as a source to empower the work of each individual, of all collaborators within a corporation, but it also empowers all attacks."
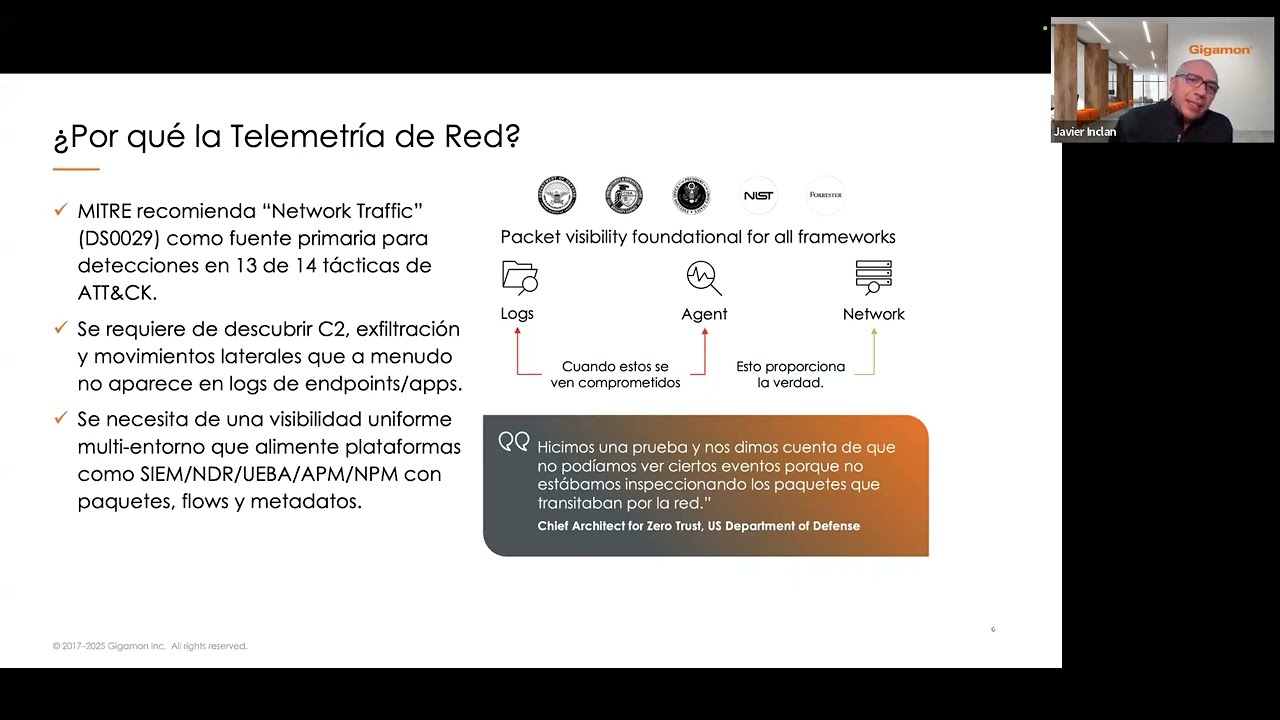
Network Telemetry Proves Essential for MITRE ATT&CK and NIST Compliance
Network telemetry is a critical data source for cybersecurity, particularly in meeting the requirements of frameworks like MITRE ATT&CK and NIST, according to Javier Inclán. Network traffic is fundamental for detecting 13 out of 14 tactics outlined in the MITRE ATT&CK matrix, serving as a primary indicator for various stages of an attack. This visibility is especially vital for securing challenging environments such as Internet of Things (IoT) and Operational Technology (OT) systems, which often cannot support traditional security agents, as well as for monitoring volatile containerized workloads and addressing blind spots in hybrid cloud architectures.
The increasing complexity of modern IT environments, including microsegmentation and the rapid deployment and dissolution of containers, creates numerous blind spots for conventional security tools. Network telemetry provides an indispensable layer of visibility, enabling organizations to detect anomalous behaviors and lateral movements that would otherwise go unnoticed. This comprehensive monitoring ensures that security platforms can effectively protect against sophisticated threats by enriching their detection and incident response capabilities with real-time network data.
"MITRE ATT&CK, on its website, indicates that telemetry is super important as a data source to identify 13 of the 14 techniques indicated by its matrix."
Network Telemetry Outperforms Logs in Detecting Sophisticated Attacks
Network telemetry is a more reliable source for detecting sophisticated cyberattacks than system logs because network traffic is far more difficult for attackers to modify, according to Javier Inclán. While logs can be altered to hide an attacker's presence, network packets are much harder to tamper with in transit, requiring significantly more effort and time. This inherent integrity makes network telemetry a primary data source for identifying advanced threats.
The MITRE ATT&CK framework, a widely adopted database of adversary tactics and techniques, emphasizes network traffic as essential for detecting 13 out of its 14 attack tactics. This includes crucial phases such as command and control communications, data exfiltration, and lateral movement within a compromised network. Effective security tools, including Network Detection and Response (NDR) systems, depend on comprehensive network visibility to function optimally, as blind spots can render even advanced solutions ineffective against determined adversaries.
"Modifying what is traveling over the network is much more complex, and many times attackers use those encrypted channels."
Network Telemetry Illuminates Blind Spots in Zero Trust Security
Network telemetry is crucial for the effective implementation of a Zero Trust security model, functioning as an illuminating light in an otherwise dark network environment, explains Óscar Acosta. The core principle of Zero Trust—"never trust, always verify"—demands continuous validation of all network activity, which traditional security layers like firewalls and authentication systems alone cannot fully provide. Observability, powered by real-time network telemetry, exposes critical blind spots and lateral movements within networks, regardless of whether traffic is encrypted or decrypted.
This deep visibility into network activity provides undeniable facts, complementing existing security platforms and ensuring adherence to frameworks such as NIST. By revealing hidden movements and potential breaches that might bypass conventional defenses, network telemetry reinforces the Zero Trust philosophy, transforming assumptions into verified certainties about network integrity. This is especially vital as threats like identity theft and compromised credentials can easily circumvent perimeter defenses, making internal network monitoring indispensable.
"Observability within the framework of Zero Trust is like that dark room where, in a first stage, to know what is around that room without having visibility, without observability, is to put a light, a bulb that will allow us to see every corner, every point, every element."
Cybersecurity Faces Evolving Threats and Challenges by 2026
The cybersecurity landscape will face escalating challenges by 2026, driven by the increasing complexity of cloud environments and emerging technologies, according to Javier Inclán. Key concerns include securely acquiring and transporting cloud traffic, addressing persistent blind spots in hybrid and multi-cloud architectures, and managing the disruptive impact of post-quantum computing on existing encryption methods. Organizations will also need to optimize data ingestion and storage to comply with long-term retention laws, which can require keeping information for up to 15 years.
Furthermore, providing rich, application-level context for security teams will be indispensable for rapidly triaging security events, moving beyond mere process identification to understand the full scope of an incident. The continuous rise of AI-driven applications and attacks also poses a significant threat, as AI can be used to generate sophisticated exploits, bias information, and compromise large language models. These evolving threats underscore the critical need for reliable network telemetry to enhance defense strategies.
"The additional challenges for 2026 are acquisition of cloud traffic and that secure transport of content. That is one of the things that I see growing."
Gigamon Boosts Observability for Critical Regulatory Compliance
Gigamon plays a fundamental role in enhancing network observability, providing 360-degree visibility that significantly strengthens security tools and aids compliance with essential regulatory frameworks like MITRE, Zero Trust, and NIST, according to Óscar Acosta. By decrypting traffic, extracting valuable metadata, and optimizing network data flows, Gigamon empowers security platforms to achieve a broader and deeper understanding of network activity. This enhanced visibility is particularly crucial for heavily regulated sectors such as banking, service providers, and government entities, where strict compliance is mandatory.
The ability to monitor and analyze all network traffic, including encrypted and lateral movements, ensures that organizations can meet their regulatory obligations effectively. Gigamon's technology acts as a foundational element, providing an independent, verifiable source of truth about network events. This allows security teams to move beyond assumptions, offering concrete facts that are necessary for robust defense strategies and demonstrable adherence to complex security mandates.
"Gigamon is that strong piece that will empower all tools to go further, to have a 360-degree radius."
Gigamon Enhances Network Observability to Combat Advanced Threats
Gigamon enables organizations to achieve deep network observability by comprehensively monitoring all traffic, thereby exposing anomalous behavior and providing crucial visibility in environments where traditional agents cannot be deployed, such as IoT and OT systems, explains Javier Inclán. The platform decrypts encrypted channels, revealing hidden lateral movements and data exfiltration attempts, even those disguised through common protocols like DNS. This deep insight transforms network traffic into an independent source of truth, making it significantly harder for attackers to manipulate compared to system logs.
By offering clear, unencrypted visibility to various security, performance, and observability tools, Gigamon significantly enhances their effectiveness. This capability is critical for identifying zero-day attacks and sophisticated threats that exploit validated internal processes. The comprehensive visibility provided by Gigamon improves security posture, optimizes application performance, and accelerates problem-solving by delivering undeniable facts about network activity, which is essential for adhering to frameworks like MITRE, Zero Trust, and NIST.
"We cannot secure, we cannot protect what we cannot see. So, if we cannot see, we are susceptible to anything that happens."
Also mentioned in this video
- The importance of observability as a current reality for 2026, emphasizing the… (0:32)
- Understand their meaning, differentiating it from mere monitoring or visibility… (1:26)
- Óscar Acosta concurs with Javier Inclán's definition, stressing that… (3:20)
- The importance of network telemetry for deep analysis and identifying the root… (7:26)
- The critical need for observability in protected and encrypted traffic,… (10:37)
Summarised from GigamonTV · 54:04. All credit belongs to the original creators. Streamed.News summarises publicly available video content.